Getting Ready for Round Three
In the wake of the Solar Winds upstream attack we find ourselves in the midst of the ProxyLogon attacks on Microsoft Exchange servers. Both of these have a high penetration in their field of victims (18,000 for Solar Winds and 400,000 for ProxyLogon). But there’s more to come and the third round is going to be even bigger.
SickCodes released a vulnerability it found on the 28th (yes, March 28th, 2021) it found in the netmask package which is part of the NPM registry. NPM stands for “Node Package Manager” which is the ubiquitous (almost universal) package manager for Node.js. Node.js itself is a framework that creates an asynchronous event-driven JavaScript runtime which is heavily used in web development. In fact, according to https://hostingtribunal.com/blog/node-js-stats/#gref there are more than 20 million websites using it, more than 1 billion downloads with 6.3 million websites in the U.S alone. Some companies that rely on Node.js are Amazon, CitiBank, Netflix, eBay, Reddit, LinkedIn, Tumblr, PayPal, Wal-Mart, and Uber but these are just the biggest ones. The vulnerability leads to server side request forgeries which leads to a whole host of attack vectors including being able to force the web server to make connections to any server the attacker chooses. The worst case is the attacker using the web server to make connections to the internal servers to which it has access.
Because Node.js uses a package manager to install modules it is very likely that the netmask packaage has been included on nearly every Node.js installation. A package manager is a piece of software that manages what components are loaded in a software framework (operating system, application environment, or runtime). In the case of Node.js developers can use NPM to find and install the components they need in an automatic way. All package managers can handle dependencies which means they will find all the pieces of code (libraries in old school speak) that a package requires. What this means is, if a developer chooses to install package A and package A also requires package B and C, and package B requires D, E, and F, and package C requires G, H, and I, the total list of packages to install are A, B, C, D, E, , G, H, and I. Here’s a real-world example:
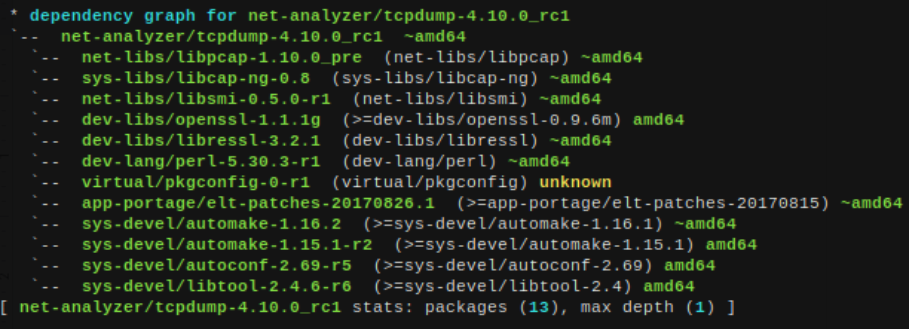
This is from my Linux system that shows to install the tcpdump package I need 12 other packages–its dependencies. What this doesn’t show is the dependencies of all those packages but with the package manager for my Linux distribution (Gentoo’s emerge) I can easily show those by adding “emptytree” which means assume nothing is installed and find all packages that need to be installed. Here’s the results:
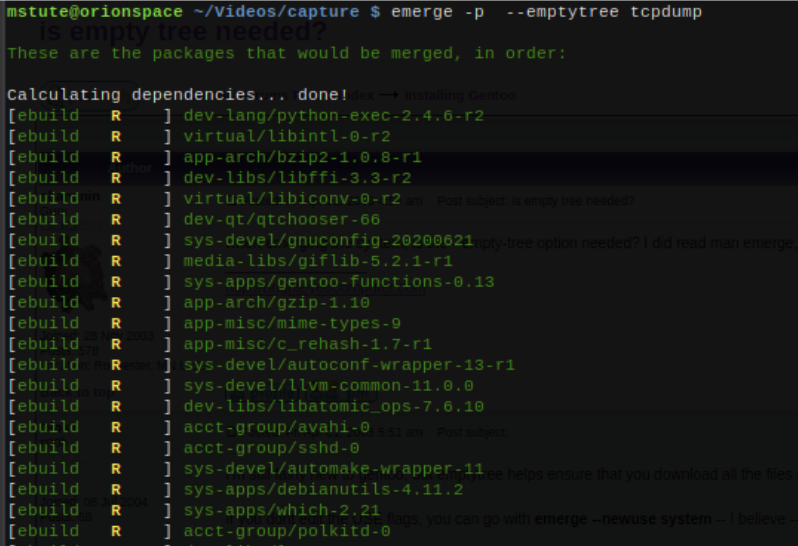
But that is just the top portion, the list contains a total 477 other packages. This might seem like a lot but tcpdump requires a console which requires an operating system kernel, but if I wanted to run tcpdump my package manager is prepared to install a whole Linux kernel, all the needed system and application libraries to support it, terminal drivers, network infrastructure, and everything else needed by the system just to run a simple console command. This just goes to show how complicated computers have become, and Node.js is no different and that is way it is very likely that netmask has been included in your Node.js runtime.
The problem with NPM’s netmask is that it is used as a very basic component for communicating on a network which is the base medium for which Node.js is designed to facilitate: deliver web content from a web server application. This is like saying that a problem has been found in spark plugs so everything using a spark plug is vulnerable. Imagine the list: cars, lawn mowers, string trimmers, chain saws, airplanes, irrigation pumps, boats, leaf blowers, generators, drones, tanks, etc. The list goes on and on, and that is exactly what the situation with netmask for Node.js. There are approximately 210,000 open source projects that use netmask from NPM. That’s already a huge list and it doesn’t even include proprietary software. As of the week of 3-16 to 3-22 (before this vulnerability was announced) netmask was downloaded over 3 million times.
Tighten those seat belts, this one is going to be big. If you use Node.js you are a target. Get with your developers and make sure they know what is happening. Make fixing this problem their number one priority. An upgrade to version 2.0.0 (though only 11 days old) fixes the problem. Do it now because the pitch is already over and the ball is already speeding to the plate.




